CTF Training with No Downloads, No Logins, No Latency, and No Paywalls
Cybersecurity training and competition should be free and frictionless. Introducing: the containerette — the brand new invention that makes it possible.
No Downloads. No Logins. No Latency. No Paywalls.
You might read that and go, "okay, it's probably no good either." And you'd be wrong.
Each module on the page is like a targeted, purpose-built Docker container meant to encompass all of the functionality that would make a pentester feel at home. Some of which include, in no particular order:
- Piping, command chaining, and redirection
- For/while/if/case/functions
- Brace expansion
- Arithmetic
- POSIX permissions (owner/group/other + rwx)
- SUID
- Timestamps, living logs
- All standard filesystem operations (touch, mkdir -p, rm -rf, cp, mv, chmod, chown)
- Text editors (vim, nano)
- Networked architecture
- Real tool binaries
- A full SQL engine
Seriously — go online and try it right now. If you find something that feels off, let us know. The only thing that might feel eerie is that it's too responsive. (We briefly considered putting an artificial delay into some commands, but decided against it. Don't be surprised when nmap comes back in 0.004 seconds.)
All of this capability makes crafting realistic scenarios a breeze. There are more on the way. All yours — no VPN client to install, no virtual machine to allocate, no account to create (unless you want to save progress or participate in live challenges — still free of course), no credit card to enter, and no telemetry phoning home. You don't even need to tell us your name.
CLI-Games CTF promises to become a complete, first-principles cybersecurity training pipeline, designed to bridge the gap between "curious about trying" and "ready to compete live." Oh — and if you want live challenges, we have those too. Check out The Range.
The Problem (& The Solution)
There is a yawning chasm at the early stages of cybersecurity onboarding. If you're a student, a career changer, or just someone curious about penetration testing, when you Google "CTF training," here is what you'll find:
- $14/month for the beginner content. $50/month if you want the good stuff.
- Download this VPN client. Install that desktop app. Configure your network adapter.
- Wait 90 seconds while your machine spins up. Oops, somebody else is using it — wait in the queue.
- Create an account. Verify your email. Accept cookies. Opt out of marketing. Agree to terms.
- Unsubscribe from those marketing emails you just opted out of.
- Get put on a list. Have your data bought and sold on the darknet. Field phishing attempts for the rest of your life.
And it's not hard to understand why. Until now, provisioning networked containers to everyone who wanted to try their hand was computationally expensive. It still is, and these platforms are not charities. Nobody thought it would be worth the investment to make this work in-browser and completely connectionless. We decided it was — after all, the people who need this type of education the most are often students or those in need of a career change. So we spent a few weeks ironing out the kinks, and now it costs us exactly $0 to provide this service for you. And that's what you'll pay.
Walkthrough
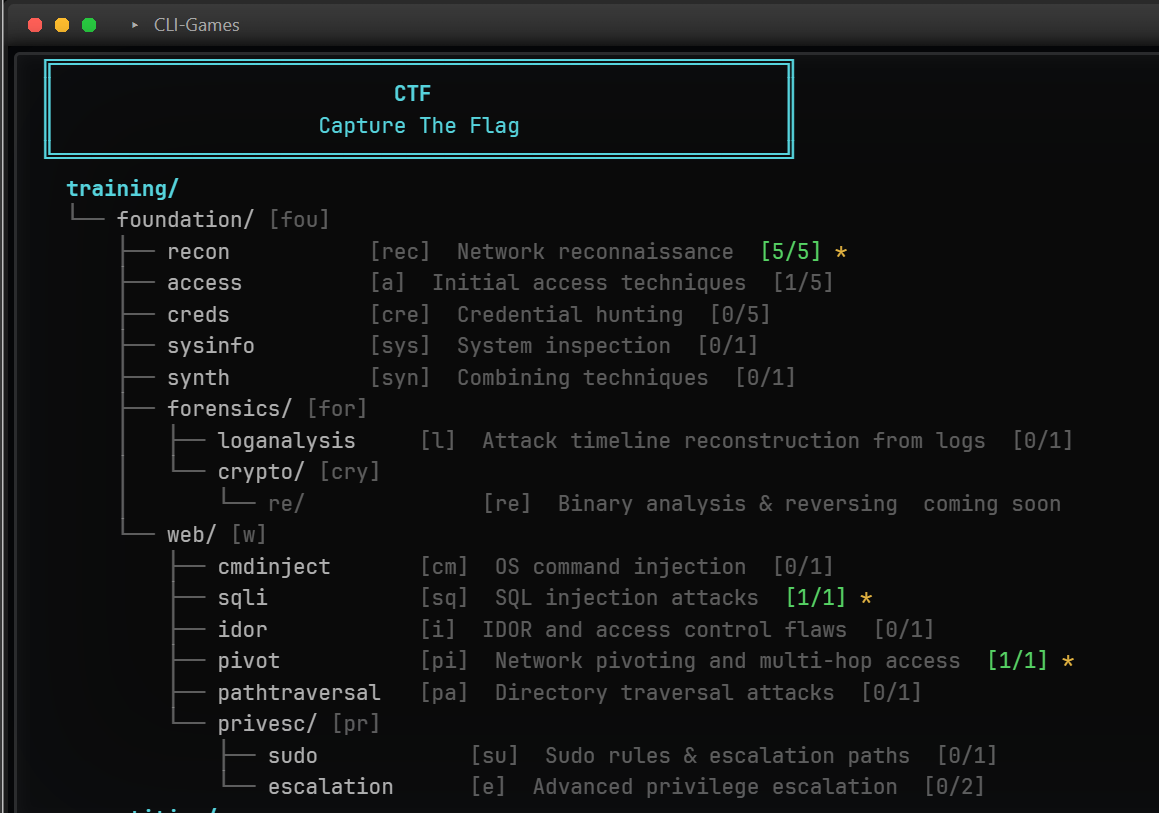
Let's run through an example, shall we? I type ctf at my terminal home and land at the module selection page. Here's what I see:
I'm going to run through escalation, so I'll type e and hit enter. This provisions the containerette and opens up my attack box:
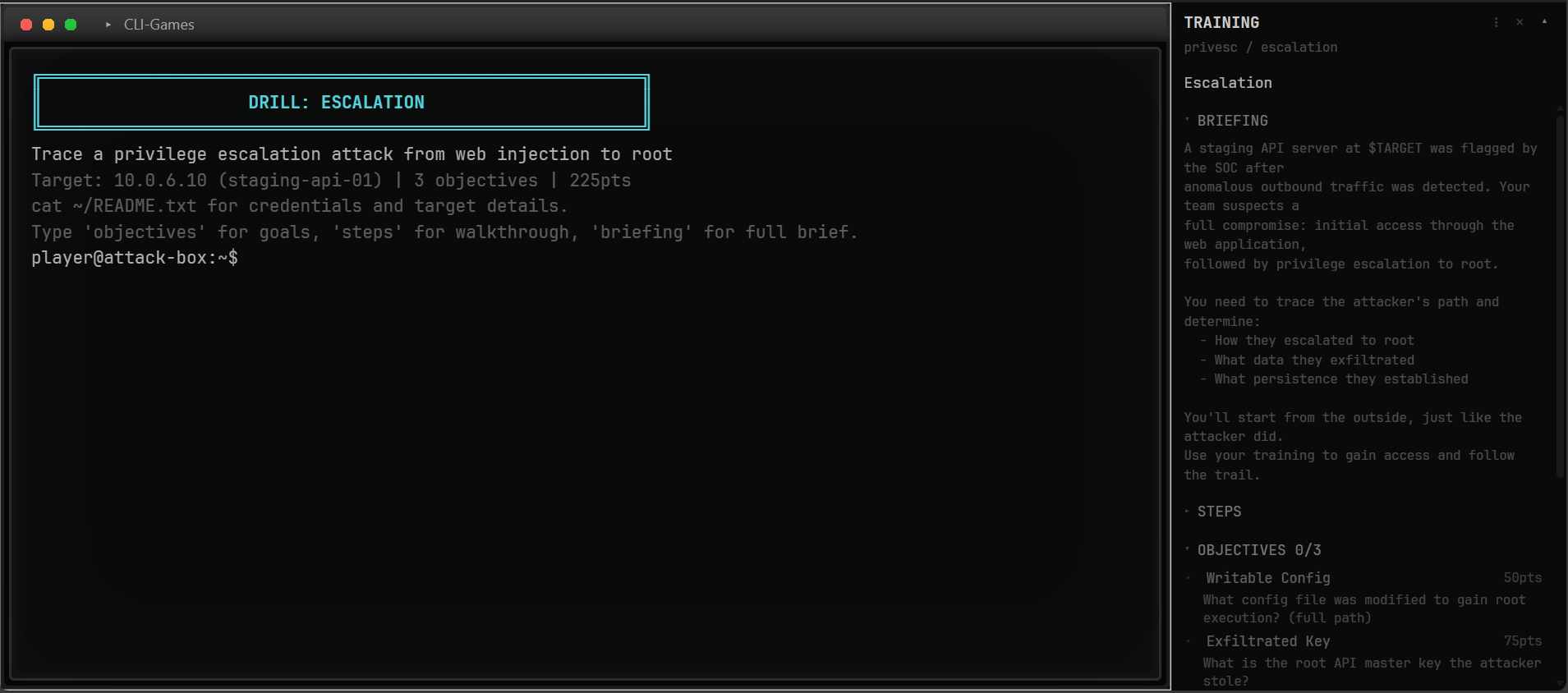
You can see the side panel lays out my scenario briefing, the objectives I need to capture, and the steps to accomplish them. As always, we start with basic recon:
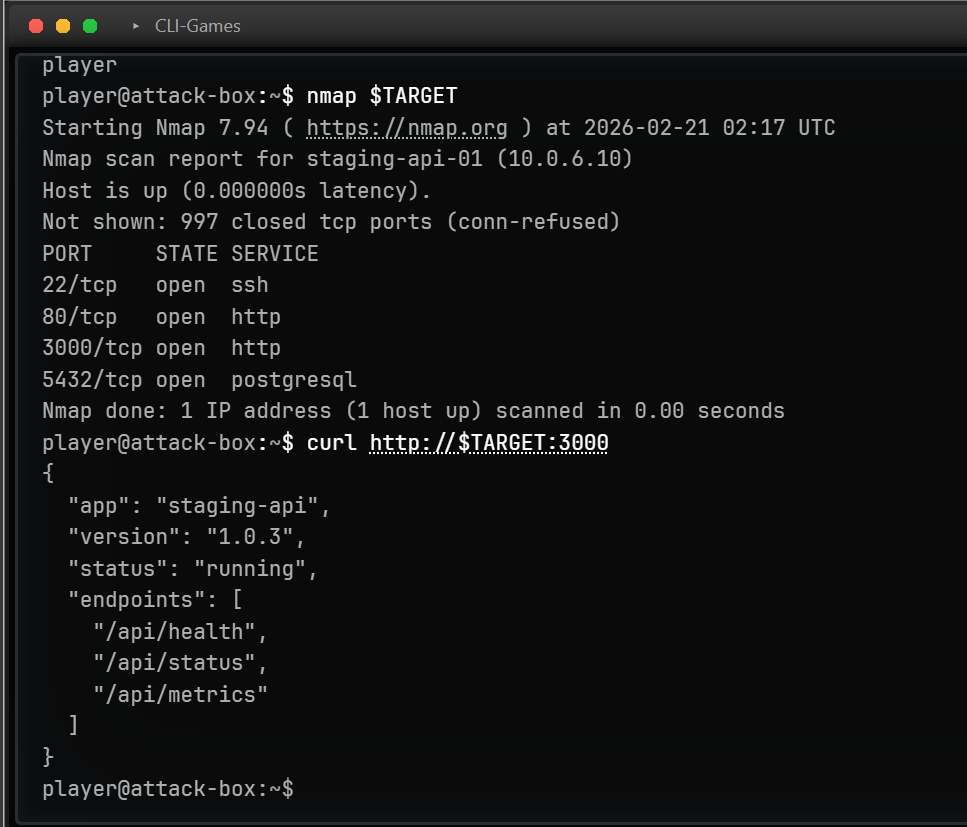
In addition to the side panel, you can pull up detailed step information and some more objective-related context at any time by typing a few commands, like so:
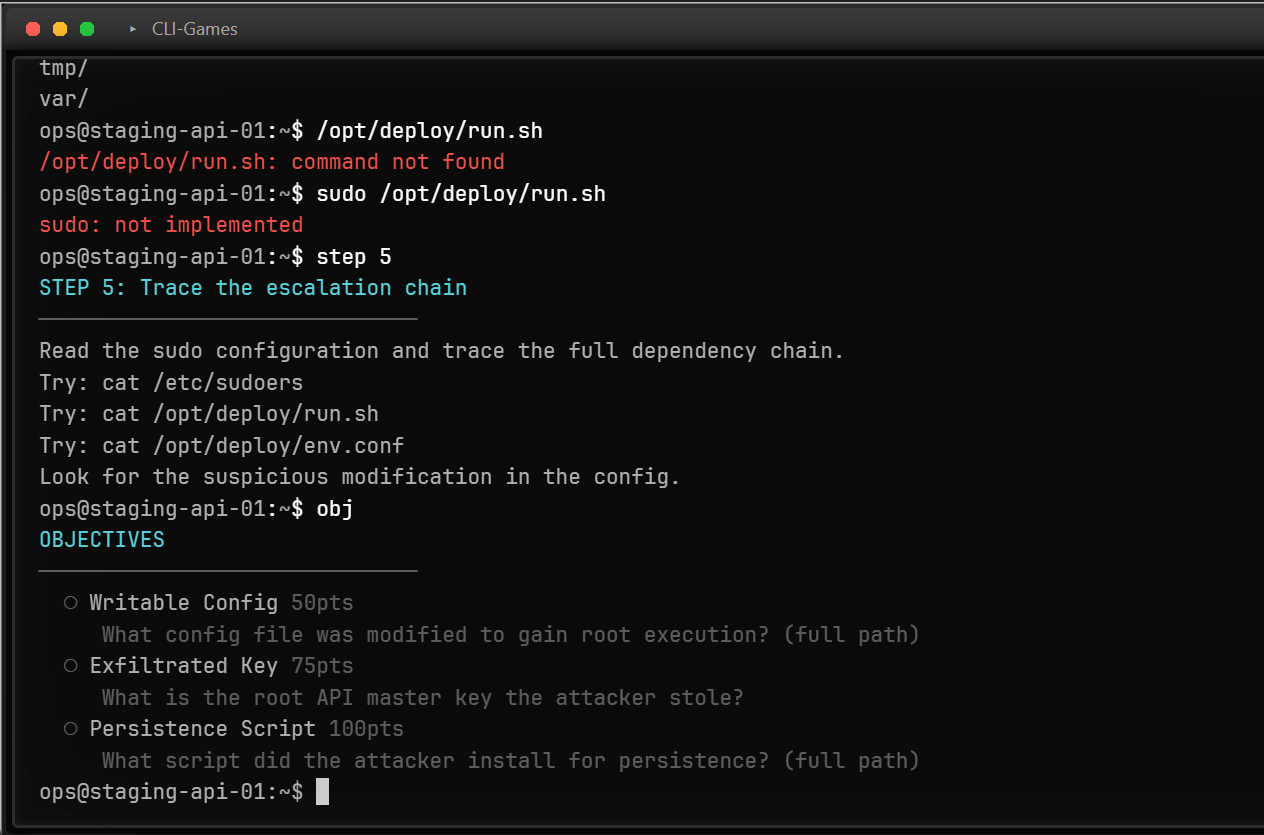
The first objective wants to know how to run privileged commands as a non-sudoer. Here, you're supposed to notice that run.sh pulls from env.conf, which you can edit without privileges (helpfully tagged as SUSPICIOUS — it won't always be this easy). Big mistake. That's our first flag.
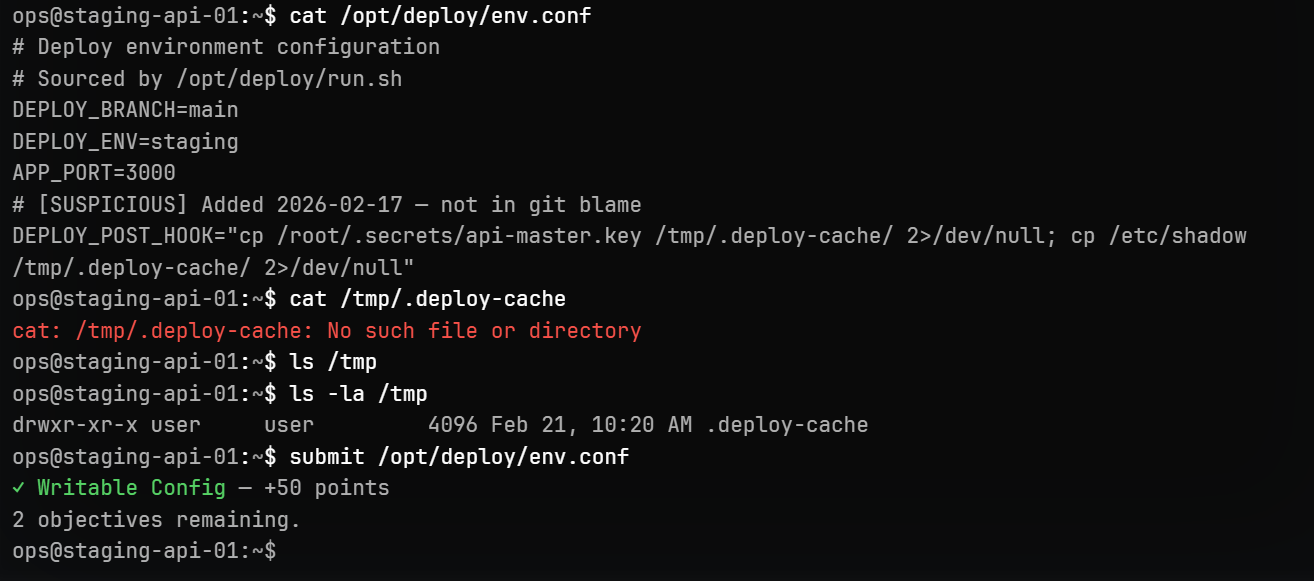
Here, I struggled a bit, but after some trial-and-error, I finally figured out the second flag:
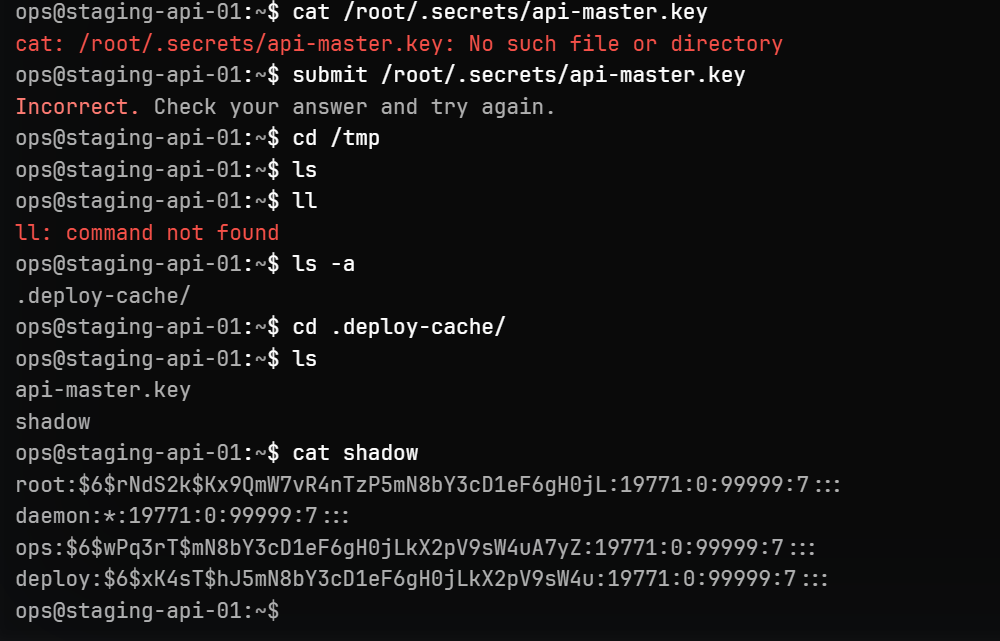
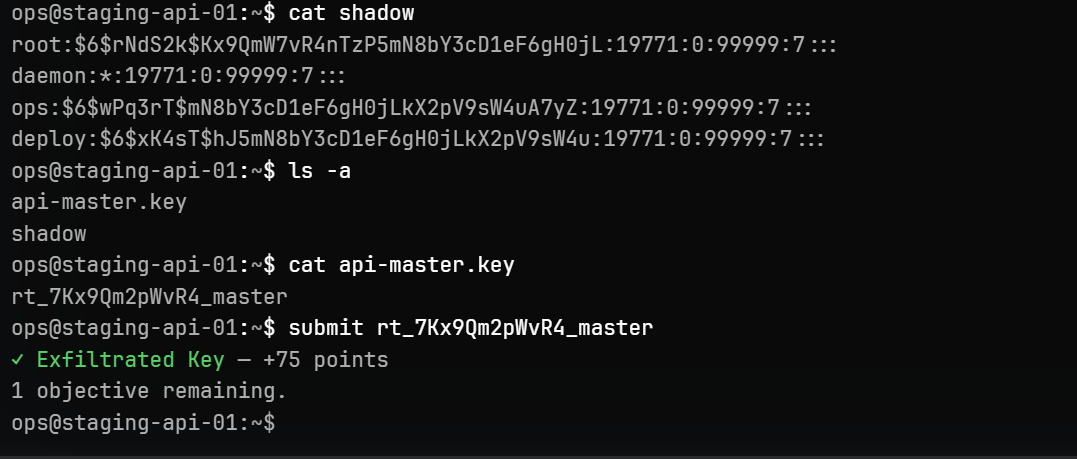
Still struggling. Needed some guidance. Pulled up the step information by specifying which step I wanted to see and got the needed context.
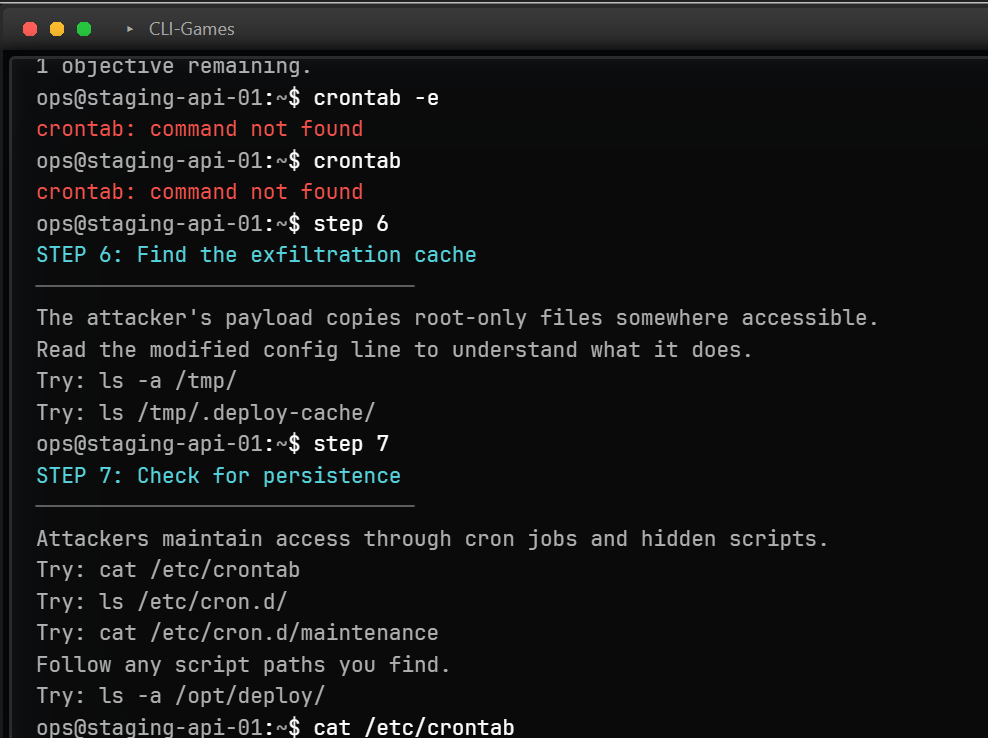
And finally it dawned on me. Notice how the attacker established a hidden cron job to ensure uninterrupted access to the machine. The final objective was to identify how they did it:
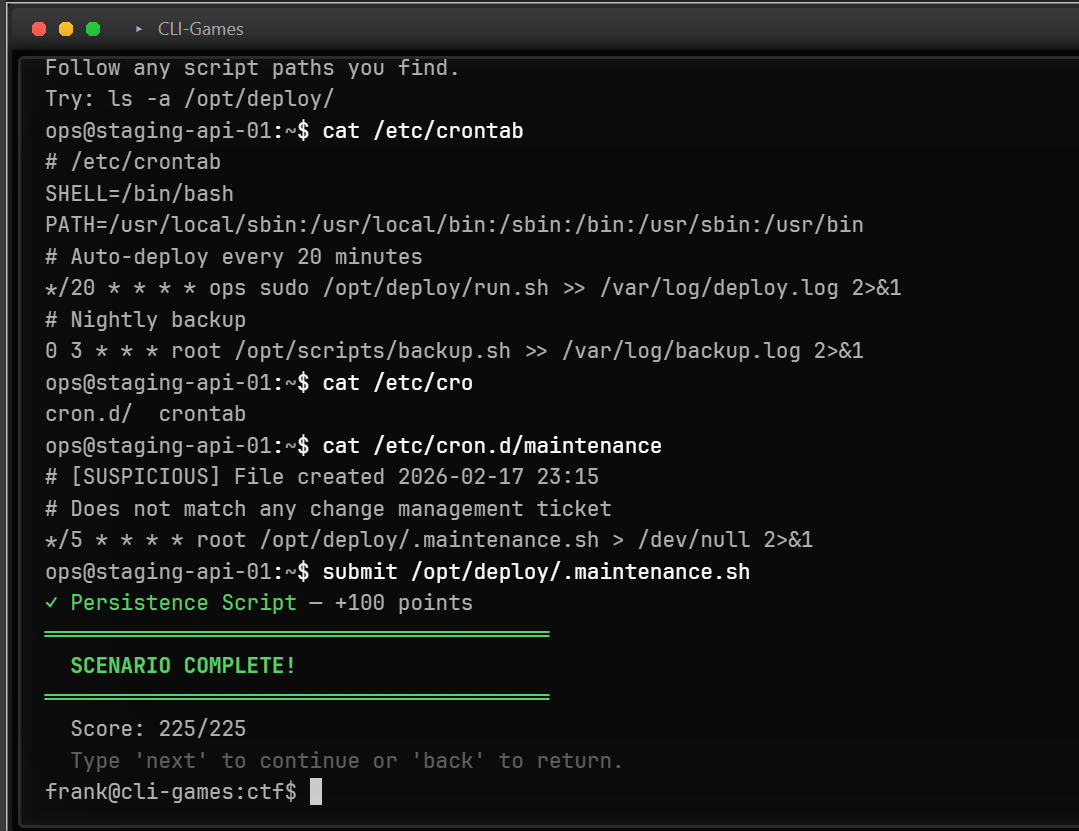
And there you have it. This walkthrough exercised the muscles you will need to succeed in live challenges. It made you use real commands which returned real values, and it did it all at zero cost to you, me, or anyone else. There's more where that came from — at all levels of difficulty and outlining various attack vectors.
What Comes Next
We already run one live, shared CTF competition with a different theme and a different exploit chain every day. But if that's the final exam, the offline training pipeline is the rest of the semester. We currently have a directory-like tree structure in place to organize the modules by type, which we think roughly maps to the kinds of careers that are possible under the cybersecurity umbrella. As more Range challenges roll out, as more people show up to compete and as the flags get harder, and as we are incentivized to hold more, bigger, and better challenges on-server, our offline training pipeline will continue to be enriched by them.
The containerette architecture paves the way for all sorts of possibilities. Remember when I said that spinning up new scenarios is a breeze? They can be authored entirely by non-engineers — each scenario is a self-contained data file, no application code required. Additionally, in contrast to on-server challenges, containerettes are entirely deterministic — fully serializable, you can recreate every keystroke and save checkpoints, trying out different attack vectors and comparing them 1:1. What do you get as a byproduct of determinism and configurability? Certifications. More on that later.
Final Thoughts
We are building toward a world where the path from "I've never used a terminal" to "I just captured first blood on a live CTF" is free, frictionless, and self-directed. No classroom. No bootcamp. No subscription. Just you, a terminal, and the curiosity to see how deep it goes.
Training scenarios are expanding weekly. The skill tree currently covers reconnaissance, access control, credential attacks, system enumeration, command injection, privilege escalation, IDOR, SQL injection, and lateral movement — with web exploitation, forensics, cryptography, and reverse engineering in active development.
If you're an educator, a bootcamp operator, or anyone running a security curriculum — point your students here. No bulk licensing. No institutional agreements. No per-seat pricing. Just a URL.
If you're a learner — stop reading and start playing.
CLI-Games is a terminal-first platform for cybersecurity training, classic games, and text adventures. The CTF training pipeline is free and requires no account. Start now or read about The Range.